Article
Cyberattacks: what good is a an armored door if we do not lock it?
It is necessary to identify risks for each organization and to exercise due diligence to care for their assets. Good security practices are daily put to the test in organizations.

Recently, a growing number of computer attacks on organizations has been noted. Examples such as attacks on Ebay and Dropbox, the hijack of credentials and passwords, or the alleged Russian attack on Hillary Clinton’s Presidential campaign resulting in the release of more than 60,000 emails from the campaign, are an emergent pattern.
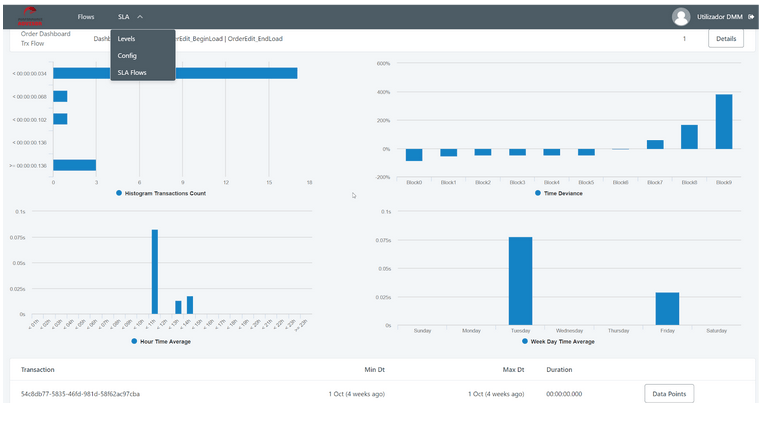
In the past week, the world suffered an unprecedented attack on its scale, according to Rob Wainwright’s statements. The attack was performed in the form of a ransomware that results not in the leak of information but in the denial of user’s access to the information contained in the encrypted files and consequent ransom demand to release the data. Above all, this attack caused panic in organizations, resulting in the suspension of activities and disconnection of the equipment’s network access, for fear of the attacks’ impact.
The response to this attack was a dramatic demonstration of the contingency plans’ value that allowed to mitigate the impact of these attacks and, most importantly, enabled organizations not to be held hostages of fear and to recover promptly from attacks.
Whatever the outcome of the current attacks is, it is a mandatory need for organizations to redefine themselves and to ensure that “everyone” knows their role in the imminence or concretization of an attack. It also demonstrated the lack of preparation of organizations, where some plans are neither tested nor validated and the best practices (e.g. update for the latest security patches) are neglected in favour of the day-to-day improvisation.
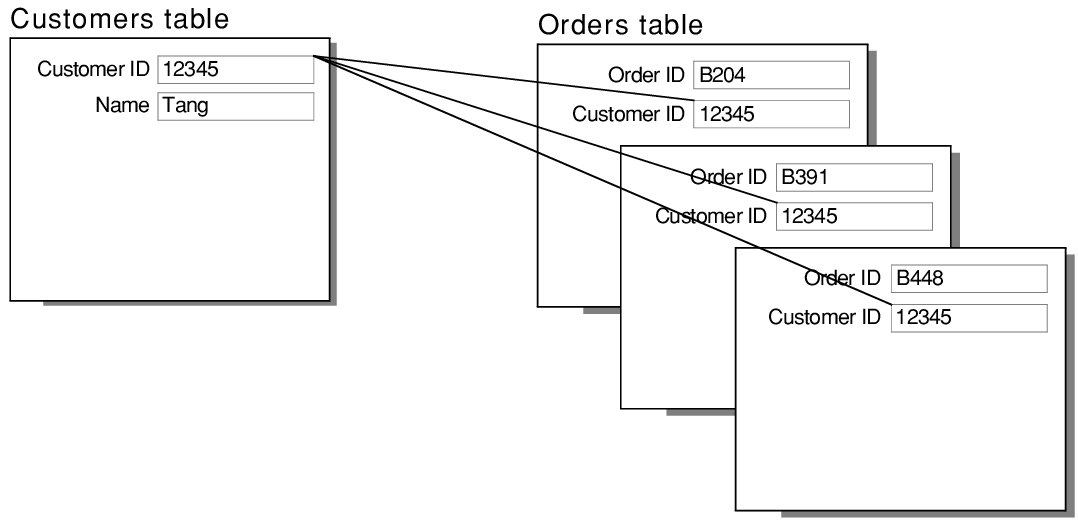
Let us think about this for a second: we live in an electronic society, in the midst of a digital transformation, where we have not only our computer, smartphone, tablet, kindle, etc… but also where the information is starting to be accessible from less usual channels like televisions, fridges, washing machines, illumination systems, etc. The truth is that controlling the physical access to organizations access is the easy part and the one that poses the least threat. The information ends up being prone to propagation within the referred channels, not always covered or controlled by our mitigation strategies.
Thereby, it is necessary to identify the risks for every organization and exercise due diligence to protect their assets. The good security policies are daily put to the test in organizations, where computers are unlocked and emails practices are not controlled.
A few years ago, inside a client’s building, we did the simple experience of “losing” a USB on purpose with a link to a website. The first access occurred 38 minutes after the loss. It served only to reinforce the lack of preparation of employees concerning this issue. This is an example of what the lack of preparation linked to a weak development of business continuity culture may imply for an organization. Prompting the question: what good is a armered door if we do not lock it?
Published on: Observador